
The evolution of wireless networks has seen the technology move towards inter-device connectivity, and the latest 5G and Wi-Fi standards are aimed at being more pervasive with the power to connect smart cities and homes. Bluetooth isn’t going to be left behind, and to this end, the Bluetooth Special Interest Group (SIG) on Tuesday announced support for mesh networking. The organisation says mesh capabilities will enable Bluetooth to offer many-to-many device communications, adding that support had been optimised for large-scale device networks.
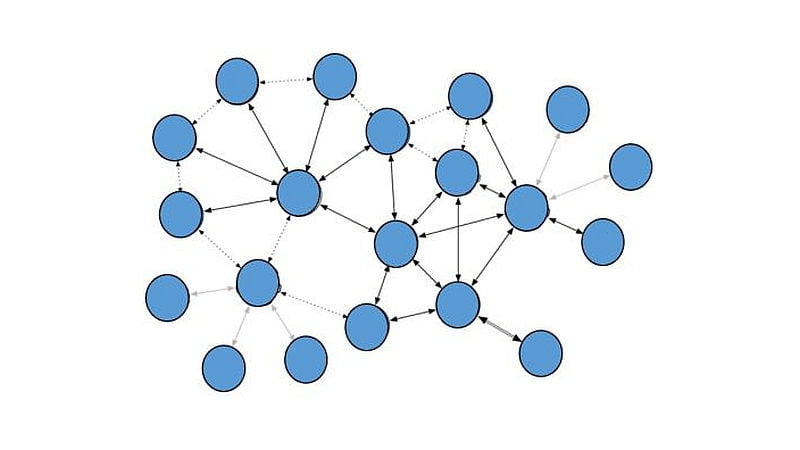
Bluetooth mesh networking uses the Bluetooth Low Energy (LE) protocol, and is compatible with Bluetooth v4.0 specification and higher. The Bluetooth SIG adds that the Bluetooth mesh networking specifications, along with tools needed to qualify products, are now available on the Bluetooth website. Notably, the standard was first previewed back in November 2014. With the technology, Bluetooth evolves from a point-to-point star network topology and makes into a mesh network that keeps on expanding as more and more mesh nodes are added.
Mesh networking capabilities of Bluetooth are claimed to be ideally suited for building automation, sensor networks, and other IoT solutions built out of as many as thousands of devices. The group is touting benefits that Bluetooth brings for many-to-many device communications, including inherently self-healing networks with no single points of failure, scalability for thousands of nodes, industrial-grade security, global interoperability, and a full-stack approach that specifies all aspects of technology from low-level radio up to the high-level application layer. As we mentioned, the new Bluetooth mesh networking standard will take on both 5G and Wi-Fi in the eyes of manufacturers for their inter-device communications, but of course, solutions integrating all three are possible.
Speaking on the launch of the Bluetooth mesh networking specification, Mark Powell, executive director for Bluetooth SIG, said, “By adding support for mesh networking, the Bluetooth member community is continuing a long history of focused innovation to help new, up-and-coming markets flourish. In the same way the connected device market experienced rapid growth after the introduction of Bluetooth Low Energy, we believe Bluetooth mesh networking can play a vital role in helping early stage markets, such as building automation and wireless sensor networks, experience more rapid growth.”
[“Source-gadgets.ndtv”]





















 The iconic white cane has helped provide empowerment and mobility for generations of visually impaired people and has now received a high-tech update courtesy of researchers at MIT.
The iconic white cane has helped provide empowerment and mobility for generations of visually impaired people and has now received a high-tech update courtesy of researchers at MIT.