Imagine you typed www.google.com into the browser on your Mac and it took you to Microsoft Bing. You’d probably be a bit confused, and maybe angry. But this doesn’t ever happen. Why is that?
The answer is because, at the heart of the design of the public Internet, is a hidden system of governance and ‘permissioning’ that makes it all work. The Internet is a public network with permissioning of some key resources. And the lessons we can learn from this have profound implications for the future of blockchain systems, especially in the enterprise.
Here’s a summary of the argument I make in this piece:
- Open, shared, general purpose, broad access networks – public networks – tend to dominate over time. But public does not imply anarchic or permissionlessness. For example, on the Internet, Certificate Authorities require the permission of operating system vendors to be trusted by their browsers, and use of specific names and numbers requires permission that derives from IANA. The Internet is a public, permissioned network.
- The analogous critical infrastructure in blockchain networks is transaction confirmation. So should it be subject to permissioning? If your goal is censorship resistance then the right to be a proof-of-work miner must be permissionless, but the tradeoff is transactions are only ever probabilistically final. If censorship resistance is not a goal then transaction finality can be achieved but the consensus providers must be known, and hence permissioned. So both public-permissionless and public-permissioned models work for blockchains, but with different tradeoffs.
- Given that censorship resistance is not a goal for most businesses, and transaction finality is, this means the optimal architecture for large-scale general-purpose business blockchains is public, permissioned.
- Corda Network, Sovrin and Alastria are examples of public, permissioned blockchain networks.
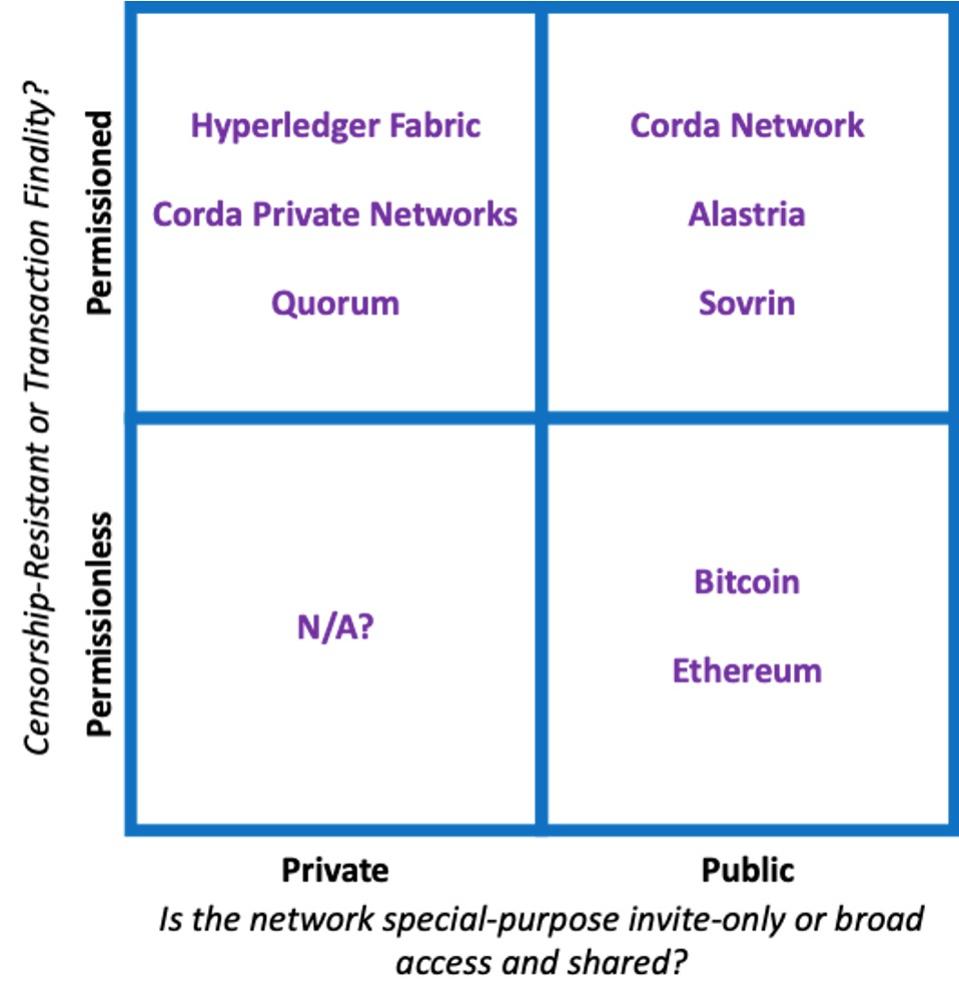
Public/Private and Permissioned/Permissionless are independent axes
Richard G Brown
The Internet is a public, permissioned network and this is why it matters for blockchains…
A worked example: how to hack Google (kinda…)
Let’s work through the example above a little. Why don’t you ever see Bing when you type www.google.com?
There are two main reasons you don’t get Bing when you want Google: the Internet’s Domain Name System (DNS) and because of Digital Certificates.
To understand why, imagine I am a bad guy trying to send all of Google’s traffic to Microsoft. How would I do it?
First, I’d need to set up a Domain Name server that gave the wrong answer whenever it was asked for Google’s address. So when somebody typed google.com into their browser, I could control where their browser went.
But if I just sent them to bing.com, that wouldn’t be enough. The padlock wouldn’t show on the browser. You would spot the error. (You do check for the padlock, right?)
To make it work, I’d have to solve the padlock problem. The technical details aren’t too important but the key thing I’d need to do is issue myself a “certificate” for google.com. And that would make the padlock show on your browser. And the reality is that anybody with a bit of technical knowledge and a few spare hours spare could do this pretty quickly.
Easy!
Well, not quite…
It actually wouldn’t work. (Sorry, wannabe hackers…)
But the reason why it would fail is of fundamental importance to the future of enterprise blockchains. And that is because it shows the critical importance of the concept of permissioning.
Why wouldn’t it work, exactly? The answer is that the Internet is a permissioned system. Potential providers of critical Internet infrastructure like DNS and Certificates need permission to have their services utilised and trusted.
We don’t often think about it this way but that’s what’s going on. The reason the trick above fails is because I can’t force you to trust my DNS server and I can’t force you to trust my ‘certificate’. In the former case I would need you or your ISP to choose to trust my DNS server. In the latter case, I would need Apple to include my Certificate Authority (CA) on the list of CAs that Macs and iPhones trust out of the box. Providers of critical services have to be invited in. They don’t get to just “rock up” and join the party without permission.
Sure… you can bring a bottle and knock on the door. But if your name’s not on the list, you’re not coming in.
If you haven’t permitted your computer to rely on my DNS server, it doesn’t matter how many lies I publish. And if I haven’t gained permission from Apple to include my Certificate Authority in its list of approved Certificate Issuers for Macs and iPhones then nobody using an Apple product will pay the slightest bit of attention to the certificates I issue. The same applies for Google with Android, and Microsoft with Windows.
In short, the Internet works because some of the fundamental building blocks of its operation – directory services, addressing, identity management – are under the control of organisations such as IANA, browser vendors and others, or are matters for individual users, who almost invariably delegate them straight back to their ISP or operating system vendor in any case. An aspiring provider of critical Internet infrastructure needs to obtain explicit permission from one or more of these groups if their service is going to be adopted or trusted. You don’t get to just fire up your service and impose your will on others.
So the Internet is a fascinating beast. It is a truly public network: open, shared, general purpose, accessible to pretty much anybody willing to pay for a connection and who can find somebody who will sell them one. And it is also permissioned: providers of critical services such as DNS or Certificates don’t get to force others to consume their service or trust them. Control – permissioning – is in the hands of the users and trusted central parties.
Censorship Resistance or Transaction Finality? Today’s reality: you can choose one.
So now turn our attention to blockchains. It should be beyond debate that, outside some special use-cases, often in finance, blockchain networks should be public. Large, open, connected, shared networks that can form organically and with minimal barriers to entry and with pricing that tracks cost. Bitcoin and Ethereum pass this test, of course. As does Corda Network, which is open to all legal entities on a cost recovery basis. And James Carlyle wrote earlier this year about how much Corda Network’s philosophy is aligned with the Alastria network vision.
But many in the Ethereum community argue that businesses shouldn’t just use public networks, they should use permissionless ones. By which they usually mean the main Ethereum network.
This sounds superficially appealing. Yet the lesson of the internet is that there can be some very tricky “gotchas” if you don’t also have some control over critical infrastructure services. If the internet was truly permissionless, I would indeed have been able to trick your computer into going to Bing when you wanted to go to Google. Or something far worse.
So the idea that businesses should bet on permissionless networks deserves scrutiny. In particular, if some of the most fundamental services requiring permissioning on the internet are routing and identity verification, are there any equivalent questions for blockchains?
The answer, it turns out, is yes. There is one very important infrastructure service: transaction confirmation.
When you submit your transaction to the network, you want it to be confirmed. But by whom? Who provides the confirmation services? What guarantee are you receiving?
On networks like Ethereum and Bitcoin, the underlying philosophy is one of censorship resistance. The networks exist to make it impossible for anybody – not even an elected government – to prevent transactions being confirmed.
And so on Bitcoin and Ethereum there is nobody, not even you, with the power to decide who confirms your transactions. Anybody with enough computing power can turn up and compete to “mine” a block containing your transaction. They have the power to confirm, but also the ability to reverse a confirmation if they amass enough computing power. A confirmed transaction can subsequently become unconfirmed.
Be in no doubt: censorship resistance is an amazing historical advance for those who need it. But there is a wicked sting in the tail: transaction confirmation on Proof-of-Work networks is inherently probabilistic. Transactions are only ever probably confirmed. If censorship resistance is your goal then this is probably a good trade-off.
But what if censorship-resistance is not your goal? What if you want to know who the parties providing confirmation services in the confirmation clusters are? What if you want to be sure that once a transaction is confirmed it stays confirmed? (Or who to sue if it doesn’t?)
And this is where the Internet gives us the answer. This is exactly the same problem as the one I opened this article with. Just like the Internet, we want blockchain networks to be public – open, shared, general purpose – whenever possible. But there are some capabilities within those public networks where there needs to be some control over who can provide them.
Permissioning – within the context of a public network – is the answer
The specific capabilities may differ between the Internet and blockchains but the solution is the same: permissioning.
Not permissioning of who can join the network. We all agree public networks are massively powerful where they can be used. But we do need permissioning of who can provide some critical common services.
This is why I think the public blockchains taking a similar approach to the internet are the ones to watch. Corda Network, Alastria and Sovrin are all examples of public networks that work in this public, permissioned way. Just as no rogue Certificate Authority on the internet can force you to accept its fake certificates, no rogue consensus provider on Corda Network, say, can force you to accept its confirmation decisions; they have to have been permissioned into that role on the otherwise public network.
You wouldn’t accept an internet connection that only probably connected you to the real Google – or to your real online banking portal. And you probably don’t want a blockchain network that only probably confirms your transactions.
Yes, public is the future. Public, permissioned. Just like the Internet.
source: forbes
